exploitbot
Autonomous penetration testing powered by local LLMs. Run inference on-device. No cloud dependency. No data leaves your machine.
Autonomous penetration testing powered by local LLMs. Run inference on-device. No cloud dependency. No data leaves your machine.
Models run natively on Apple Silicon via MLX. No API keys, no cloud round-trips, no content filtering. All inference stays on your hardware.
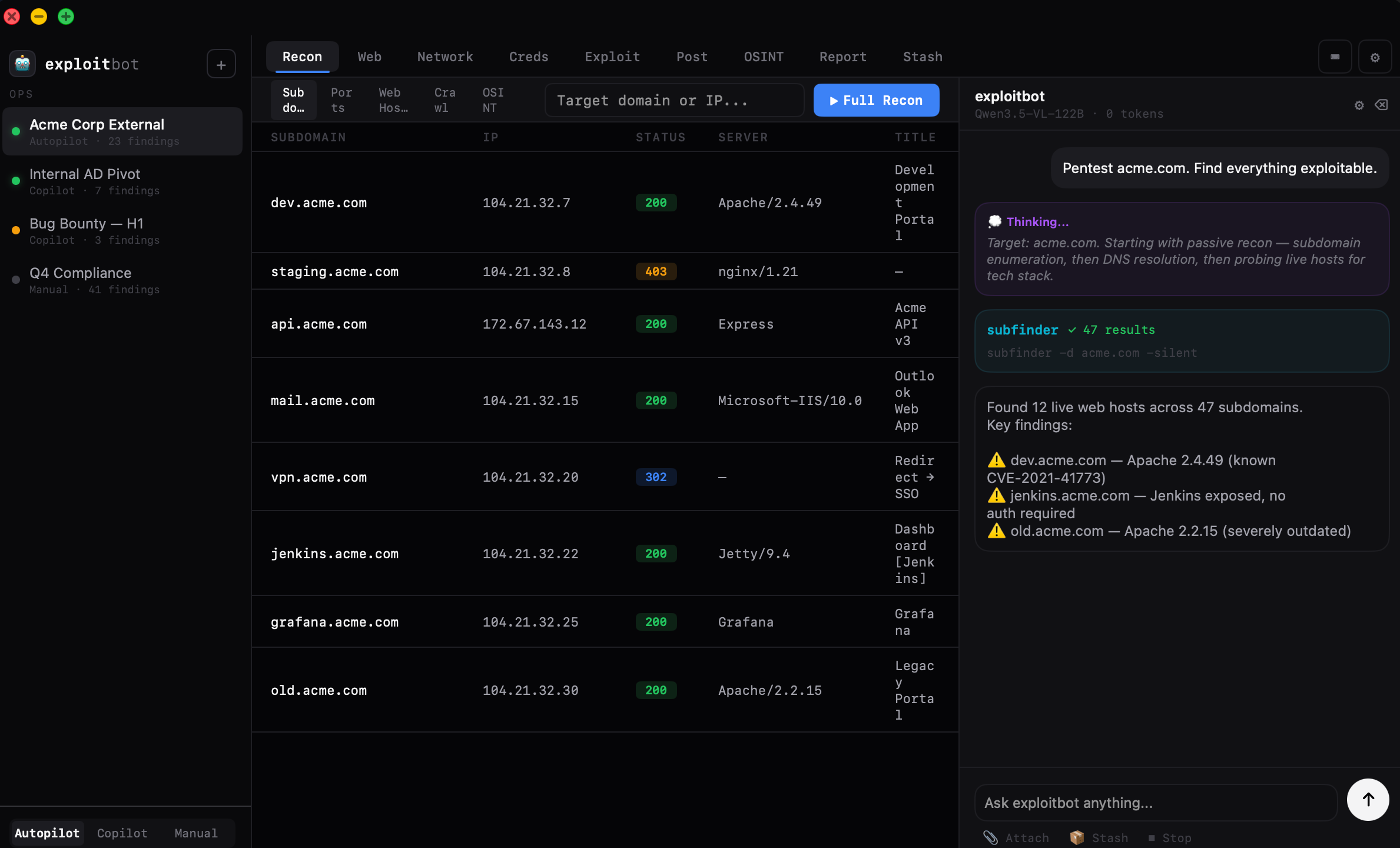
Each engagement gets a named workspace. Switch between clients and targets without losing context. The model retains full history across every tool tab.
Describe what you need in natural language or configure tools directly. The AI handles orchestration while you maintain full control over execution.
Share artifacts between engagements. Credentials, host lists, payloads, and findings persist in a searchable store accessible from any op.
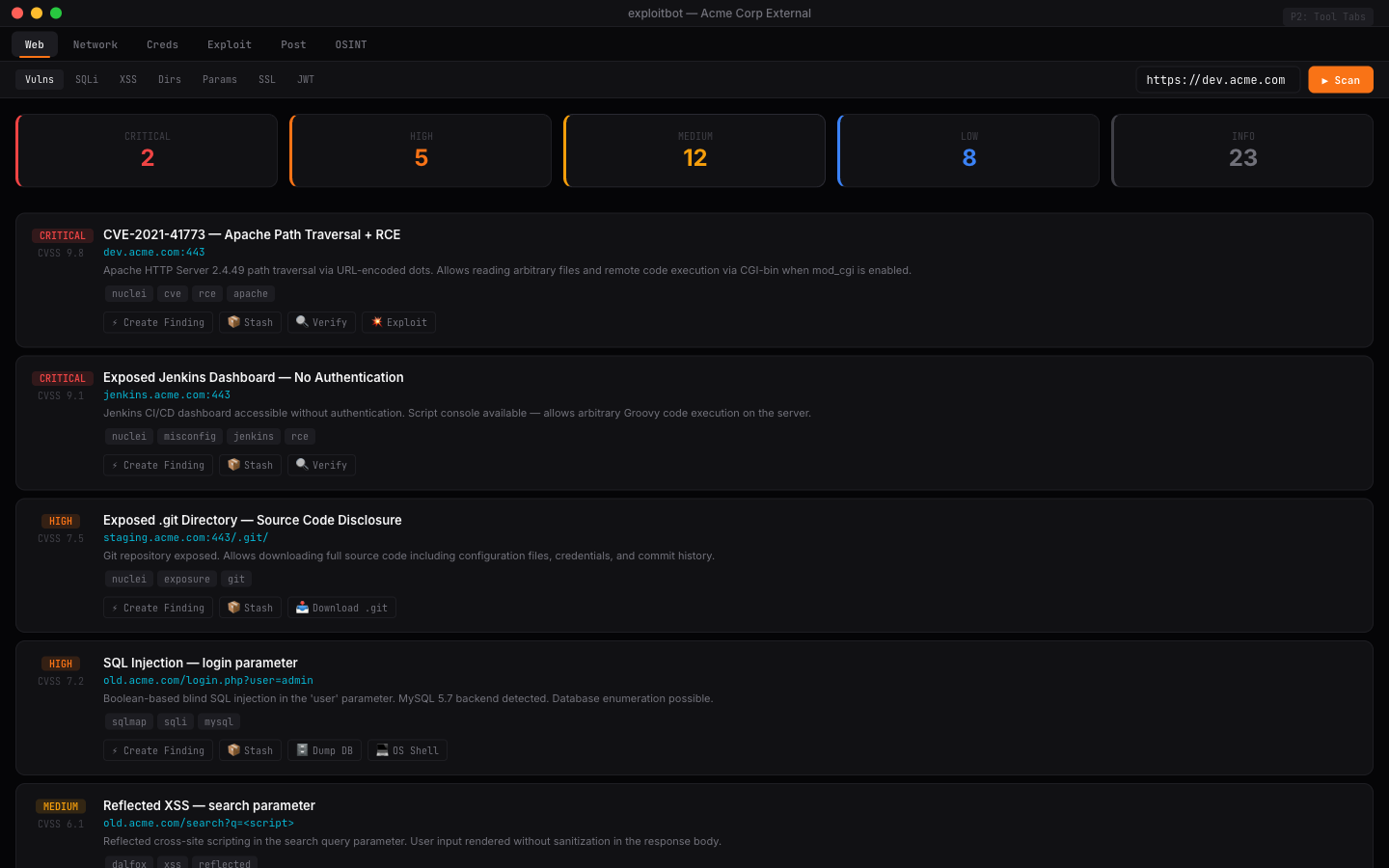
Findings capture full attack chains with evidence and impact assessment. Generate client-ready reports in PDF, Markdown, or HTML with CVSS scoring.
Built with SwiftUI. Native rendering, system animations, and blur materials. Runs as a first-class Mac application, not a browser wrapper.
Subdomain enumeration, DNS resolution, port scanning, service fingerprinting, web technology detection, and crawling.
Template-based vulnerability scanning, SQL injection, cross-site scripting, directory enumeration, parameter discovery, and fuzzing.
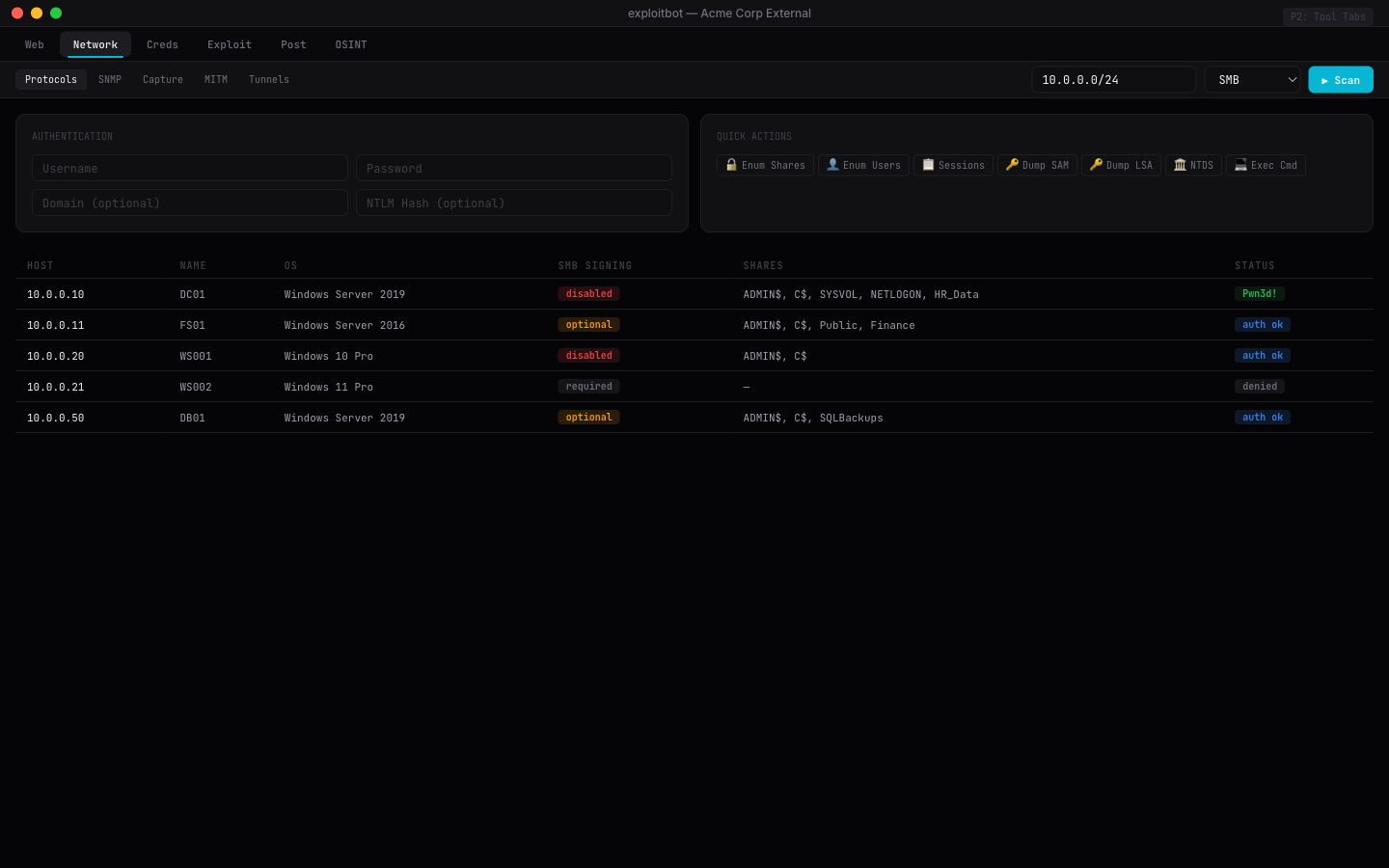
Windows protocol enumeration, SMB share mapping, SNMP discovery, packet capture, MITM, and network tunneling.
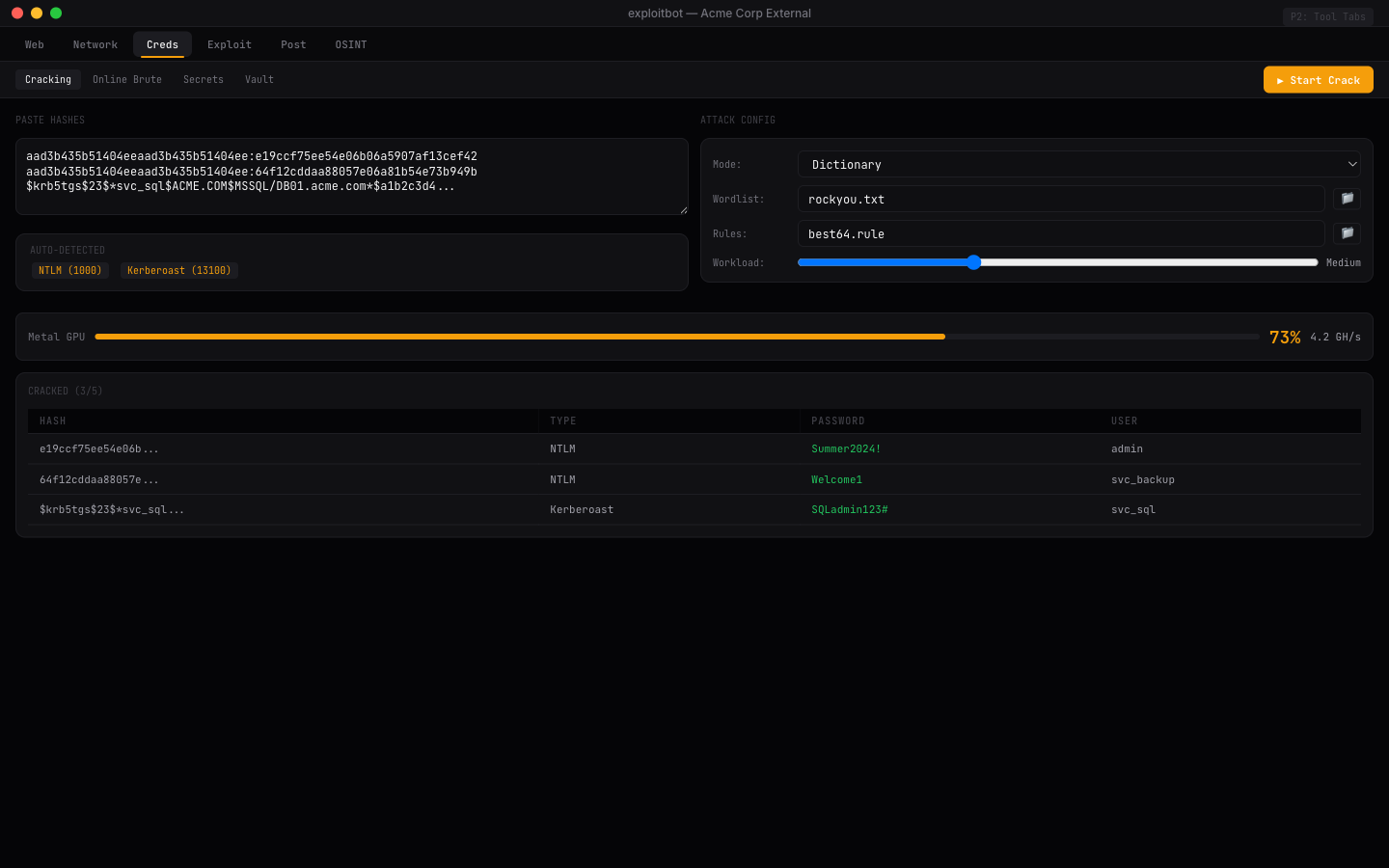
GPU-accelerated hash cracking, online password attacks, hash identification, wordlist management, and secret scanning.
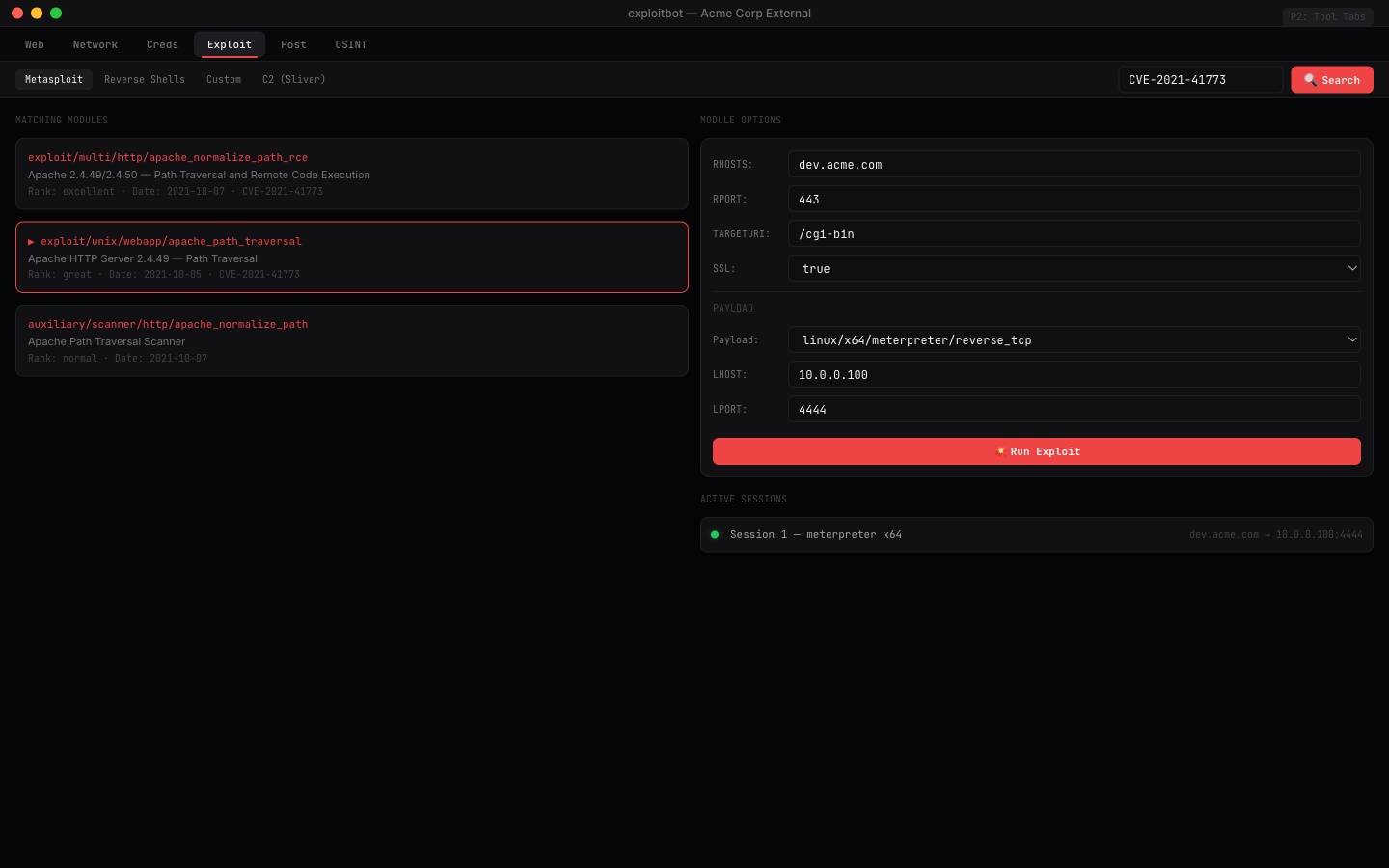
Module browsing, payload generation, session management, reverse shells, and post-exploitation frameworks.
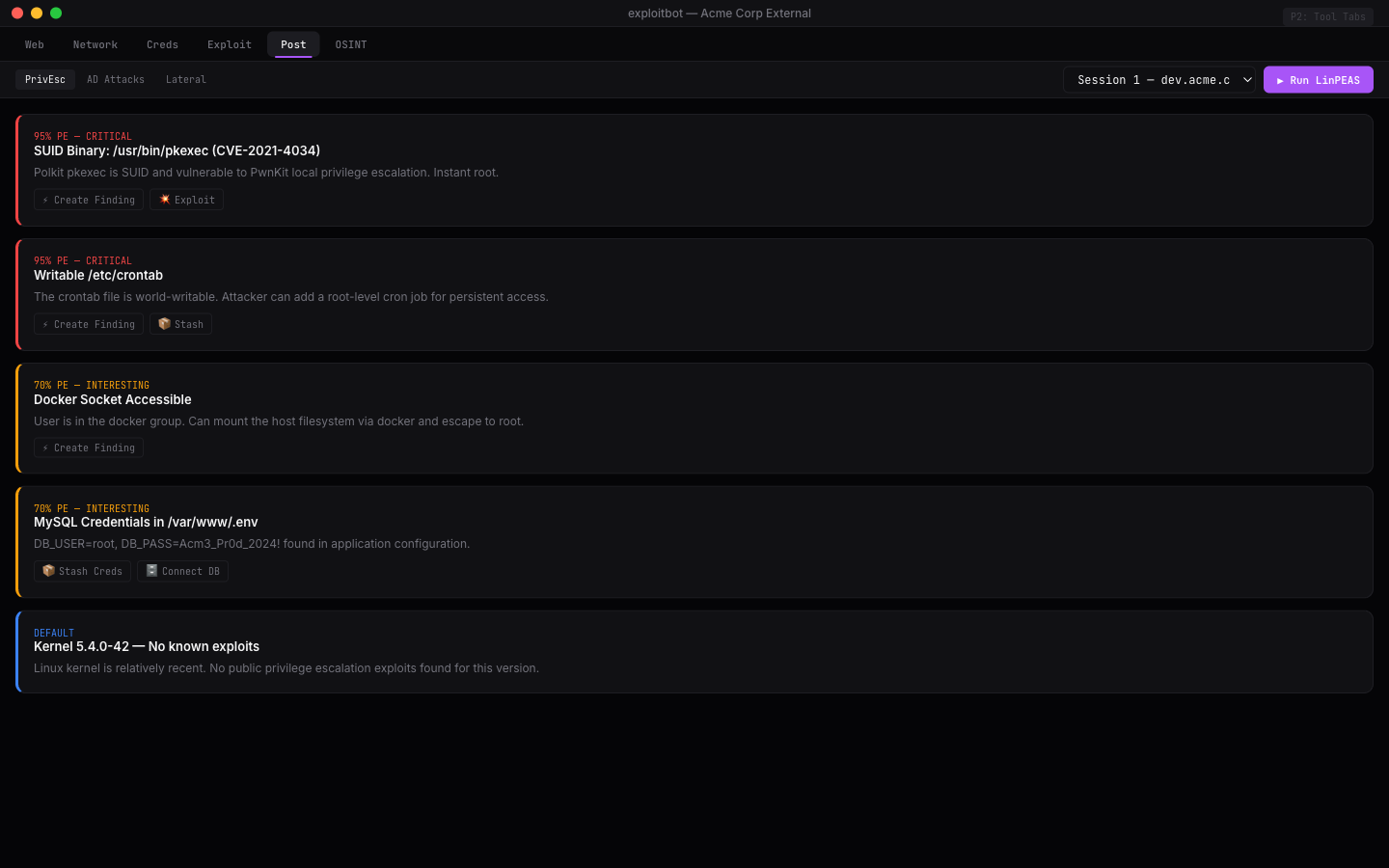
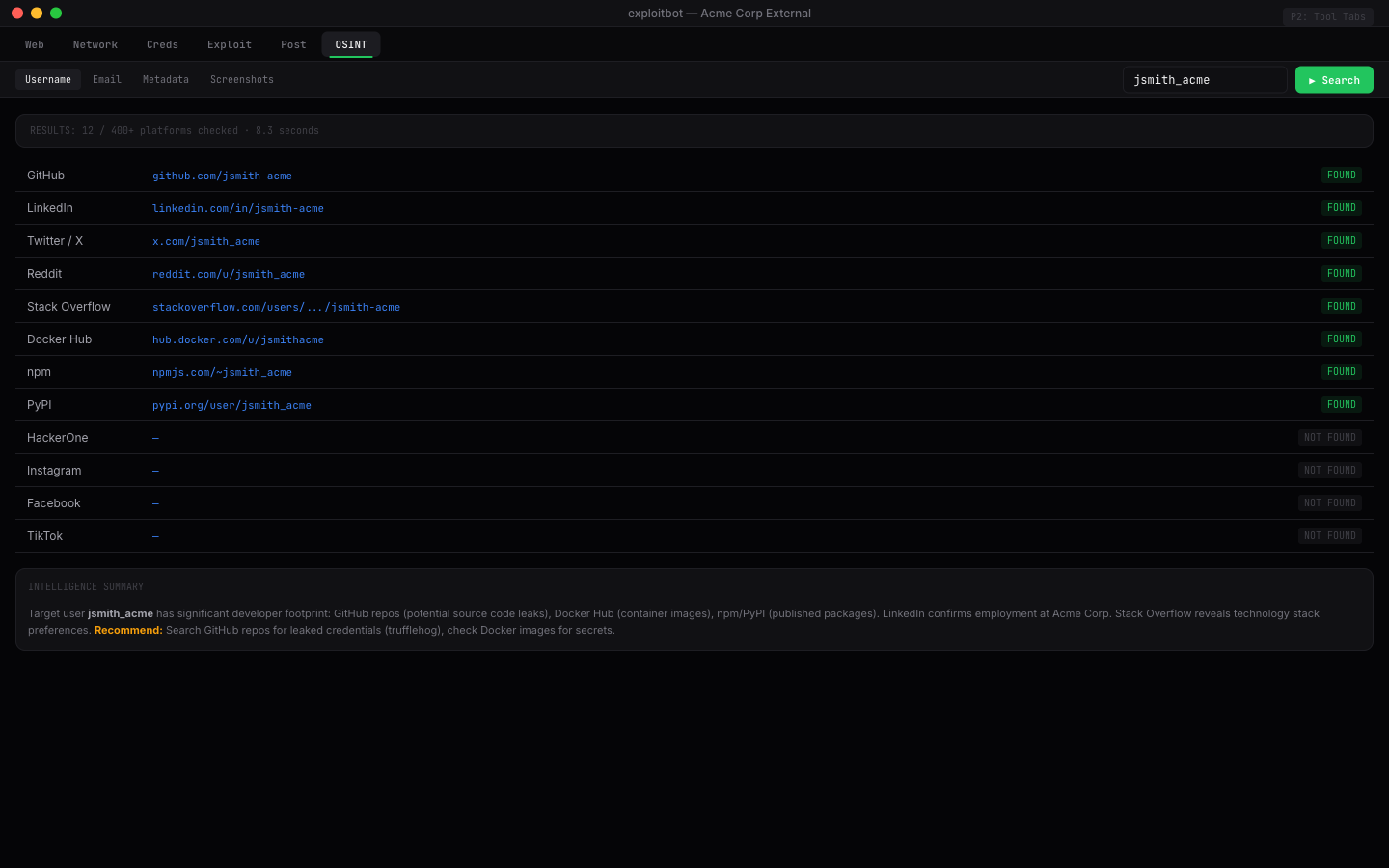
Username enumeration, email reconnaissance, privilege escalation auditing, AD attack paths, and metadata extraction.
Persistent artifact storage across engagements. Drop findings from any tool into a searchable, typed store.
Every confirmed vulnerability is tracked with full attack chain documentation, from initial access to impact.
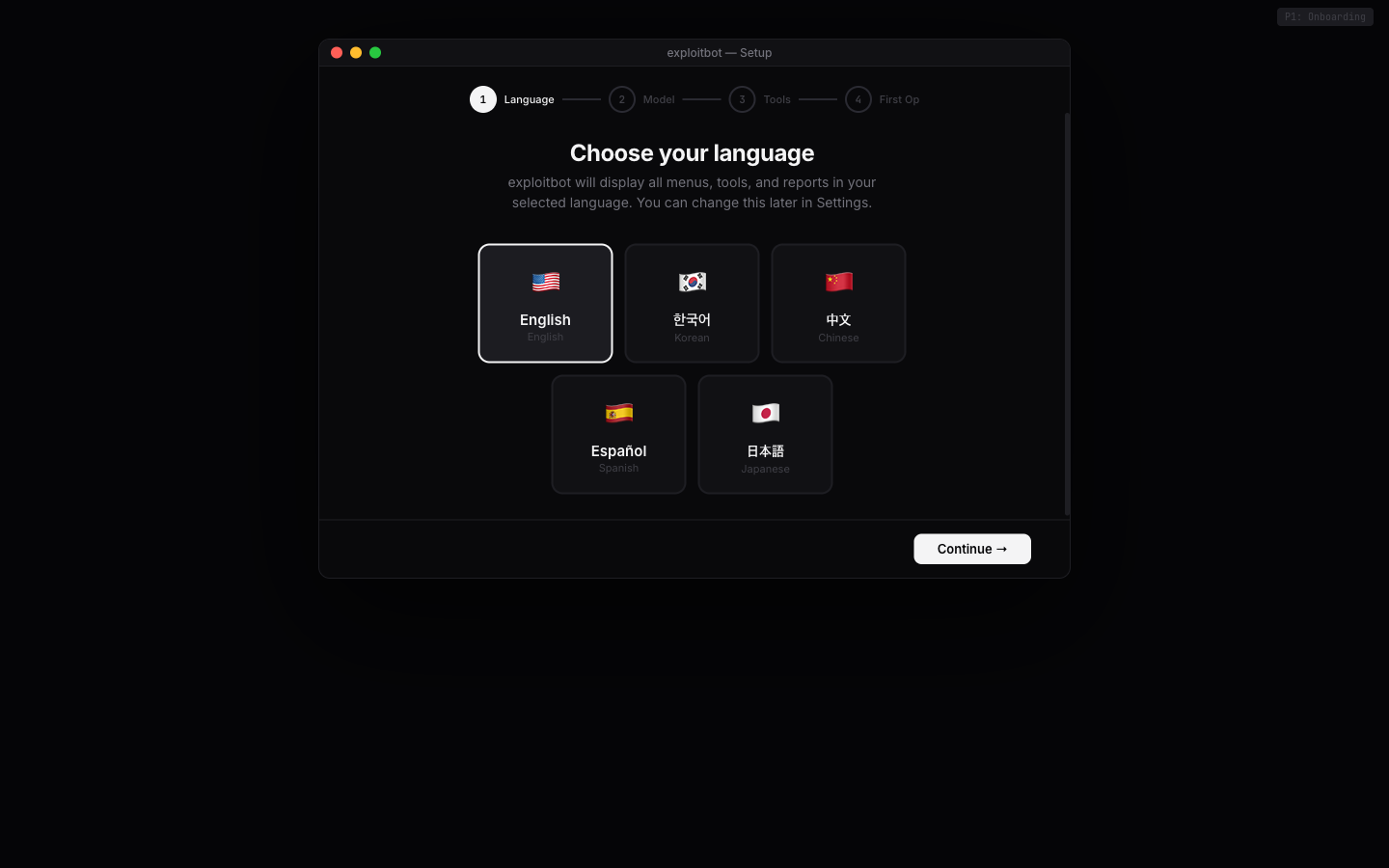
Download the DMG. Select a model. Begin an engagement.